
Imagine a world where you don't need a bank to prove you have money or a government office to prove you own a piece of land. That's the core promise of Blockchain Network Architecture is the structural design and organizational framework that allows a decentralized, distributed ledger to function securely without a central authority. It isn't just one piece of software; it's a sophisticated blend of cryptography, game theory, and distributed systems that ensures everyone in a network agrees on the truth, even if they don't trust each other.
Since Satoshi Nakamoto released the Bitcoin whitepaper in 2008, this architecture has moved far beyond just digital currency. We've seen it evolve from a simple chain of blocks into complex, modular systems capable of powering global supply chains and decentralized finance. But to really understand how it works, you have to look under the hood at the components that keep the whole thing from collapsing.
The Core Building Blocks of the Network
At its most basic level, a blockchain isn't a single entity but a collection of Nodes, which are individual computers that run the blockchain software. Depending on their role, these nodes do different things. Full nodes act as the librarians, keeping a complete copy of the entire history of transactions. Light nodes are more like index cards-they only store essential headers to verify transactions quickly. Then you have validator or mining nodes, the heavy lifters that actually process new transactions and add them to the ledger.
The data itself is stored in Blocks. Each block contains a group of transactions and a header. This header is the secret sauce of security; it contains a timestamp, a nonce, and a hash of the previous block. This creates a chronological chain. If a hacker tries to change a transaction in an old block, that block's hash changes, which breaks the link to every subsequent block. To fix it, they'd have to recalculate every single block that followed-an almost impossible task given the computing power required.
To make searching these blocks efficient, architects use a Merkle Tree. Instead of scanning every transaction in a block, the system hashes pairs of transactions repeatedly until only one root hash remains. This allows a node to verify if a specific transaction exists in a block without needing to download the entire ledger, which is a huge win for scalability.
How the Network Agrees: Consensus Mechanisms
In a centralized system, the bank decides which transactions are valid. In a decentralized architecture, the network needs a Blockchain Network Architecture strategy to reach agreement, known as a consensus mechanism. This is where the "game theory" comes in-incentivizing honest behavior while making cheating expensive.
The most famous is Proof of Work (PoW), used by Bitcoin. Here, miners compete to solve a complex mathematical puzzle using the SHA-256 hashing algorithm. The first one to find the answer wins the right to add the next block and earns a reward. It's incredibly secure but slow, processing only about 7 transactions per second (TPS) with blocks appearing every 10 minutes.
To solve the energy and speed issues of PoW, Proof of Stake (PoS) emerged. Ethereum made the switch in September 2022. Instead of burning electricity to solve puzzles, validators "stake" their own currency (32 ETH for Ethereum) as collateral. If they validate fraudulent transactions, they lose their stake. PoS is significantly faster and more energy-efficient, though it introduces different risks regarding wealth concentration.
| Feature | Public (e.g., Bitcoin) | Private (e.g., Hyperledger) | Consortium (e.g., R3 Corda) |
|---|---|---|---|
| Access | Permissionless (Anyone) | Permissioned (One Org) | Permissioned (Group of Orgs) |
| Speed (TPS) | Low (7 - 45) | High (Up to 3,500) | Medium-High (1,000 - 5,000) |
| Decentralization | Very High | Low / Centralized | Partial |
| Trust Model | Trustless | Trusted Authority | Shared Trust |
The Blockchain Trilemma: The Eternal Tug-of-War
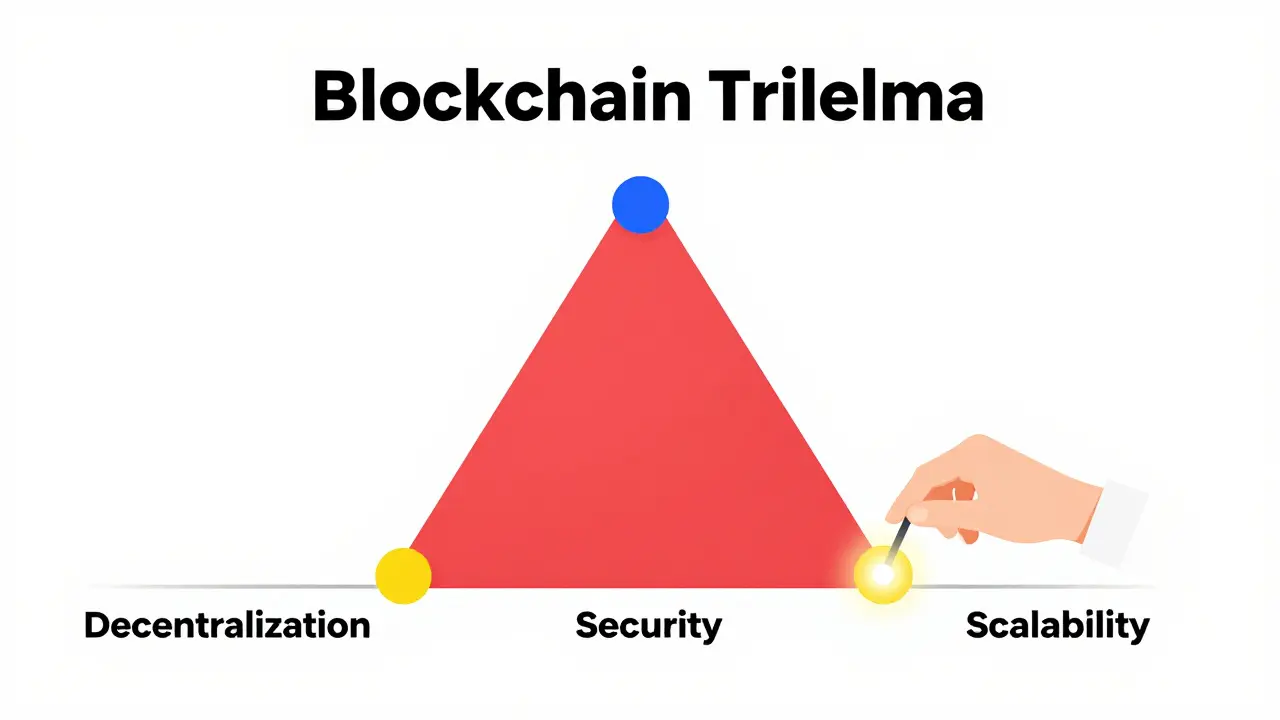
If you're wondering why we don't just have one "perfect" blockchain, it's because of the Blockchain Trilemma. Proposed by Vitalik Buterin, this theory suggests that a network can only optimize two of three properties: decentralization, security, and scalability. If you want extreme security and decentralization (like Bitcoin), you sacrifice speed. If you want massive throughput (like some private chains), you usually have to sacrifice decentralization by limiting the number of nodes.
Modern architecture is trying to cheat this trilemma through "Layered Solutions." Instead of putting everything on the base layer (Layer 1), developers build Layer 2 solutions. These act as a fast lane for transactions, settling the final balance on the secure L1 periodically. For instance, the Ethereum Dencun upgrade in March 2024 introduced proto-danksharding, which slashed Layer 2 fees by roughly 90%, bringing costs down from over a dollar to just a few cents per transaction.
Modular vs. Monolithic Design
For a long time, blockchains were "monolithic," meaning one network handled everything: execution (processing transactions), settlement (finality), and data availability (storing the data). This is like a restaurant where the chef also takes the orders, cleans the floors, and does the accounting. It's inefficient.
The new trend is Modular Blockchain architecture. This approach separates these functions. A project like Celestia, for example, focuses exclusively on data availability. By letting other specialized chains handle the execution and consensus, modular networks can hit staggering speeds. While traditional chains struggle, modular setups have seen testnet performance reaching 10,000 TPS or more.
This modularity is why we're seeing a shift toward heterogeneous ecosystems. Instead of one giant chain, we'll likely have a web of specialized chains that talk to each other via cross-chain bridges and messaging protocols. However, this introduces a new vulnerability: bridges have become a prime target for hackers, accounting for a massive chunk of the $1.7 billion lost to exploits in 2023.
Practical Implementation: The Developer's Reality
Building on these architectures isn't a walk in the park. For a software engineer, the learning curve is typically 6 to 12 months. You can't just use standard web logic; you have to master Solidity (for Ethereum) or Rust (for Solana and Polkadot) and understand elliptic curve cryptography.
One of the biggest hurdles is "gas optimization." On networks like Ethereum, every operation costs a fee (gas). If your code is inefficient, the transaction becomes too expensive for users. This has led to a massive surge in the use of development frameworks like Hardhat and Truffle, which help developers simulate and test their code before deploying it to a live environment where a single bug can lead to millions of dollars in lost funds.
Then there is the hardware problem. If you want to run a full Bitcoin node, you need about 500GB of storage. But if you want to run an Ethereum archive node-which keeps the state of every account at every single block-you're looking at over 15TB of data. This high barrier to entry is exactly why the industry is pushing toward lighter, more modular node architectures.
What is the main difference between a public and private blockchain?
A public blockchain is permissionless, meaning anyone can join, read the ledger, and participate in consensus (e.g., Bitcoin). A private blockchain is permissioned, meaning a single organization controls who can join and validate transactions, which results in much higher speeds but significantly less decentralization (e.g., Hyperledger Fabric).
Why is the Blockchain Trilemma important?
It explains the fundamental trade-offs in network design. It posits that a blockchain cannot be perfectly decentralized, perfectly secure, and perfectly scalable all at once. Architects must choose which two to prioritize based on the network's goal-for instance, Bitcoin prioritizes security and decentralization over speed.
How does a Merkle Tree improve blockchain performance?
Merkle Trees allow nodes to verify if a transaction is included in a block without downloading the entire block. By using a hierarchy of hashes, the system only needs a small "proof" (a few hashes) to confirm a transaction's validity, which is critical for lightweight nodes and scalability.
What is the difference between Proof of Work and Proof of Stake?
Proof of Work requires miners to spend computational energy to solve a puzzle to validate blocks. Proof of Stake replaces energy-intensive mining with a system where validators lock up (stake) their own tokens to earn the right to validate. PoS is generally faster and uses far less electricity.
What are modular blockchains?
Modular blockchains break the network's responsibilities into separate layers: execution, settlement, and data availability. Instead of one chain doing everything, different specialized chains handle different tasks, which allows the network to scale to much higher transaction speeds (TPS).
Jason Davis
12 04 26 / 01:44 AMMerkle trees are basically the only reason light clients even work lol. Without them you'd be downloadin gigabytes just to check if a transaction went through which is just plain stupid for mobile apps. Alot of people forget that the hash tree structure is what actually makes the verification logrithmic
Samson Selleck
12 04 26 / 09:38 AMThe discourse surrounding the 'Trilemma' is often reduced to a pedestrian understanding of trade-offs. In reality, the transition from monolithic to modular architectures represents a paradigm shift in state management. The implementation of proto-danksharding is merely a palliative measure for data availability bottlenecks, not a definitive cure. One must acknowledge that the inherent latency in cross-chain messaging protocols introduces a systemic fragility that the author glosses over with alarming brevity. The ontological distinction between execution and settlement is where the actual intellectual rigor resides, yet the narrative here remains stubbornly superficial. Most users lack the cognitive framework to appreciate the elegance of a Celestia-based DAG structure, preferring instead the comforting simplicity of an L2 wrapper. Truly, the intellectual bankruptcy of the current 'web3' developer cohort is evidenced by their obsession with TPS over actual Byzantine Fault Tolerance. We are merely rearranging deck chairs on the Titanic if we ignore the cryptographic vulnerabilities of the bridges themselves. It is a tragedy of errors played out in Solidity.
Amanda Faust
12 04 26 / 11:27 AMeveryone knows l2s are just centralization in a fancy dress
Tracie and Matthew Hartley
14 04 26 / 06:36 AMlol imagine actually trustin a 'modular' chain when its just more places for things to break. its all just a scam to get more VC money anyway
Will Dixon
15 04 26 / 05:35 AMit's a bit confusing at first but basically just think of it like a big shared spreadsheet that nobody owns. its cool stuff once u get the hang of it
ssjuul z
17 04 26 / 03:38 AMTotally agree with the point about modularity! 🚀 It's the only way we actually hit mass adoption levels! Let's goooo!
Kelly Cantrell
18 04 26 / 10:47 AMFunny how they mention 'governments' in the beginning. They want us on these digital ledgers so they can track every single cent we spend in real time. It's not about freedom, it's about a digital cage. They'll just flip the switch on your 'stake' the moment you say something they don't like. Wake up people, the 'decentralization' is a lie to get us to build the infrastructure for our own surveillance state. This is exactly how the globalists operate, promising autonomy while tightening the leash. I'll stick to cash and gold thanks.
logan bates
20 04 26 / 10:29 AMAs long as the tech is developed and secured right here in the US, I'm fine with it. We need to dominate this space before other countries take the lead. America first in tech or we lose the whole game.
Akshay Gorad
20 04 26 / 18:41 PMI appreciate the detailed breakdown of the consensus mechanisms. It provides a very helpful perspective for those of us entering the field from a different background. The distinction between PoW and PoS is often misunderstood in general discussions.
Hope Johnson
22 04 26 / 02:09 AMWhen we consider the blockchain as a social construct rather than just a technical one, we start to see that the real value isn't in the speed of the transactions, but in the shift of trust from institutions to mathematics. This is a profound philosophical transition that challenges our very notion of authority and validation. If we can build systems where the truth is derived from collective consensus rather than a centralized decree, we are essentially rewriting the social contract for the digital age. I believe this opens the door for a more inclusive form of governance where the barriers to entry are lowered and the transparency is absolute, allowing us to move toward a society rooted in verifiable truth rather than inherited power. It's a journey of learning how to trust without needing a middleman to vouch for us, which is perhaps the most human evolution of the last century.
Artavius Edmond
22 04 26 / 02:53 AMMan, this is a great read! I'm just vibing with the idea of a web of specialized chains. Sounds way more organic than one giant monster chain anyway. Cheers for the info!
Rima Dinar
23 04 26 / 07:37 AMFor anyone struggling with the concept of gas optimization, please remember that it is a gradual learning process and you should not feel discouraged if your first few smart contracts are inefficient. It takes a lot of patience to understand how the EVM actually processes opcodes, but once you start visualizing the cost of each storage slot, everything starts to click into place. I highly recommend practicing on testnets first so you can see the gas costs without risking any real capital, and don't be afraid to read through the documentation of Hardhat repeatedly until the logic becomes second nature to you. Keep pushing forward and you will definitely master it!
Prasanna Shembekar
24 04 26 / 00:32 AMomg the bridge hacks are literally a nightmare lol i lost so much sleep over my funds last year it was pure chaos
Jessie Tayaban
25 04 26 / 18:28 PMOMG the part about the 15TB for an archive node is INSANE!! 😱 Like who even has that kind of space on their laptop?? i would literally crash my whole computer just trying to sync that thing lol!
Rebecca Violette
25 04 26 / 20:33 PMi cant even deal with the fact that i have to pay gas fees just to move my own money its so unfair honestly
Carroll Foster
27 04 26 / 01:37 AMOh sure, let's just trust 'cross-chain bridges' which are basically the digital equivalent of crossing your fingers and hoping the guy with the key doesn't wake up with a gambling debt. Absolute genius design there! I'm sure the 1.7 billion lost is just a 'minor scalability hurdle' in the eyes of the architects. Can't wait for the next 'revolutionary' upgrade that fixes the last one's failure!
Lauren Abrams
27 04 26 / 02:14 AMIt's interesting how the energy consumption of PoW is always the main point of contention, but the centralization of stake in PoS is rarely discussed with the same intensity.
Scott Fenton
28 04 26 / 21:56 PMThe technical description provided regarding the Merkle Tree is accurate. It is indeed a fundamental component for achieving efficient verification within a distributed system.
Agnessa Dale
29 04 26 / 09:43 AMThis is such a hopeful look at the future of finance! I really believe we're on the verge of something that will help millions of people get access to banking for the first time.
Terrance Hausmann
30 04 26 / 02:20 AMI think we should all try to be a bit more patient with the newcomers in the space. It's a steep learning curve for everyone and we can all help each other out. If we focus on the shared goal of innovation instead of arguing over which chain is 'the best,' we'll actually get somewhere. Maybe we can start a community guide for the basics of Rust and Solidity to make it less intimidating for the next wave of devs. Let's just keep the vibes positive and keep building together!